Prudent homeowners lock their homes.
Why do so many businesses not do the same with their IT?
We hear this refrain often from prospects, “It won’t happen to me. I don’t have any ‘valuable data’ that cybercriminals would want. I don’t need all that security stuff.”
Not so fast.
Sure, some highly visible companies are big game trophies for hackers wanting to build their reputations. However, most breaches never make the news and happen to entities like yours that are just low hanging fruit for criminals picking off an easy score.
We help you keep the bad guys out.
Realtime Cyber Threats
Waident helps you take a strategic and serious approach to your cybersecurity.
That means assessing threats, determining vulnerabilities, and mitigating risks consistent with your risk tolerance and culture.
The options can be daunting, but our risk experts guide our clients through a disciplined risk assessment and add the appropriate security solutions where needed.
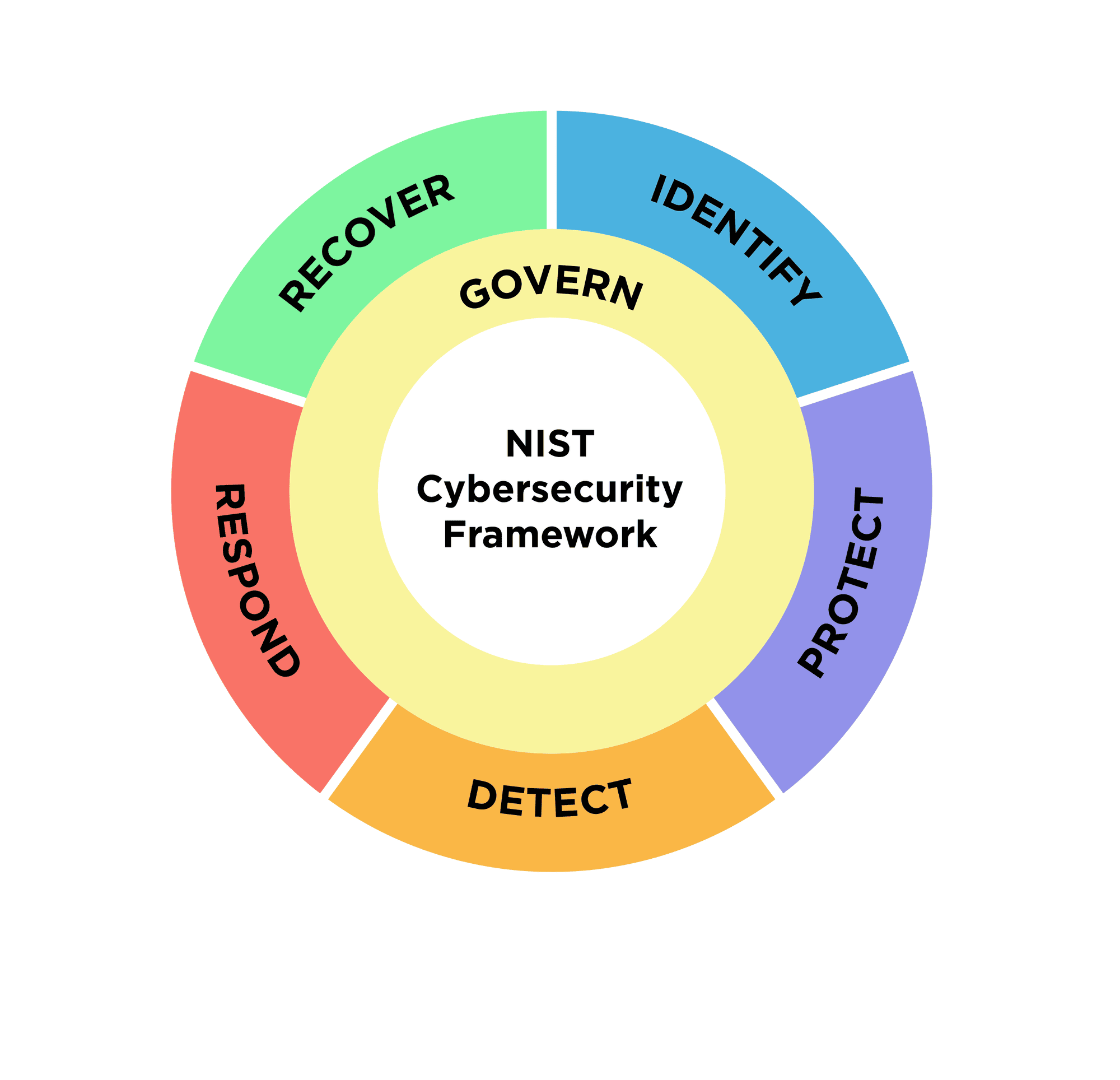
NIST – The Industry Standard
Waident uses the NIST Framework to help you strategically manage and mitigate cybersecurity risks consistent with your risk tolerance and culture. The National Institute of Standards and Technology (NIST) model includes five high-level security functions:
- Identify
- Protect
- Detect
- Respond
- Recover
- Govern.
These categories represent the pillars of a successful and holistic cybersecurity program. They help organizations categorize risk management efforts and inform management decisions.
1. Identify
The Identify function structures the organization’s management of the cybersecurity risks to systems, people, assets, data, and capabilities. Then, the organization can prioritize its efforts, consistent with its risk management strategy and business needs.

Security Review
You can’t solve a problem that is undefined. We assess your overall security strength and help you start implementing best practices. Most breaches happen because the little things were being ignored.

Risk Assessment
Our security experts perform a high-level SANS 20 review of your IT infrastructure and business processes to identify cybersecurity concerns, help lock things down, and address any vulnerabilities.

Penetration Testing
This is an advanced, social-engineered, deep dive into your IT infrastructure and your users’ behavior. More advanced than the Risk Assessment, Penetration Testing provides greater insight into your security risks from the human side.
Compliance Management
Waident assists and manages the process of monitoring and assessing systems to ensure they comply with industry security standards, as well as corporate and regulatory policies.
2. Protect
The Protect function outlines safeguards that ensure you can deliver critical infrastructure services like email and office tools and enables you to limit the impact of a potential cybersecurity event.

Next-Generation Firewall
Most companies have some form of “set it and forget it” firewall that generally works as a preliminary barrier for internet security, but may not be sufficient for specific threats your industry or your company faces. Next-Generation firewall protection provides.

Enterprise-level Multi-Factor Authentication (MFA)
It takes the concept of MFA a step further, catering to the needs of larger organizations. It’s designed to enhance security across an entire enterprise network, which typically involves numerous systems, applications, and user accounts.

Office 365 Security and Compliance Management
We help clients manage Office 365 account security through the built-in Secure Score module. Secure Score is a security analytics tool that uses Microsoft’s best practices points system to determine risk areas, develop mitigation steps, and improve your security posture with minimal user impact.

Advanced Email Protection
Most ransomware infections happen because a user clicked a link or attachment in an email. Filter and clean bad messages before they ever make it to an inbox.

Advanced AI-based Anti-Virus/Anti-Spyware
This file-based security tool is a new breed of AI-based application that takes your anti-virus and anti-spyware to a higher level.

Security Awareness Training
Most security breaches are caused by humans. Leading companies continually educate their employees about evolving security threats and best practices—and the nasty effects of clicking bad links in emails.
Secure Cloud Backups and Ransomware Backups
Backups ensure that your business can recover the files and applications you need to keep the business running after an unexpected disruption. Local backups provide quick data restoration, while cloud backups offer an offsite storage solution, protecting your data from onsite threats such as fires or floods.
Are you sure your business is safe?
3. Detect
The Detect function outlines the activities and tools that identify the occurrence of a cybersecurity event.

Managed Detection and Response (MDR)
MDR is a fully-managed 24/7/365 service delivered by experts who detect and respond to cyberattacks targeting your computers, servers, networks, cloud workloads, email accounts, and more. This service syncs through the specific Advanced Antivirus/Antispyware that Waident recommends.

Real-time Network Security Monitoring
Most security breaches are discovered 9 months after they happen. A SIEM tool (Security Information & Event Management) collects system logs and machine data from across your IT environment to provide a comprehensive view of an organization’s IT security.

IT Infrastructure Vulnerability Monitoring and Alerting
Keeping all of your systems up to date with the best possible security patches is a Herculean effort to do manually. A monitoring and alerting system ensures you are as secure as possible.

Dark Web Monitoring and Alerting
The Dark Web is an unindexed area of the internet and hotbed for criminal activity—selling of hijacked username/passwords, addresses, and social security numbers along with other bad behavior. Real-time monitoring of the Dark Web lets you know if an employee’s email address is affected, the time and location of a breach, and even a leaked password, so you can prevent problems.
Mobile Device Management (MDM)
MDM allows IT administrators to control, secure, and enforce policies on smartphones, tablets, and other endpoints. just like they manage your computers. This is a standard requirement for some compliance and cyber insurance.
4. Respond
The Respond function includes the appropriate activities that address a detected cybersecurity incident and contain its impact.
IT Helpdesk and Support
We act as your virtual technology support department, supplying assistance to end-users whether it’s at home or work. We provide support for anything related to technology:
- Computers
- Printers
- Peripherals
- Phone systems
- Smartphones
- Email programs
- Operating systems
IT Strategy
We approach IT in a strategic, proactive, and disciplined way to develop what we call “Resilient IT.” Resilient IT helps our clients bridge to their desired future state while avoiding daily technology fires or major IT fiascoes along the way.
Resilient IT is driven by:
- a people-first, tech-second mindset,
- a comprehensive understanding of system interdependencies,
- extensive documentation
- systematic preventive testing
- proven troubleshooting protocols and processes
5. Recover
The Recover function identifies appropriate activities to maintain resilience and restore any capabilities that were impaired due to a cybersecurity incident.
Post-Security Breach Incident Response
Statistics show that most companies begin operating as if “We’re back to normal.” before they have fully identify the extent of a breach and closed hole that caused it. Post-security breach forensics ensures the damage has been stopped, locates its root cause in order to fix it, and provides the insights to learn from it.
- Are you sure you’re IT is secure and there is no lingering threat?
- Does some regulatory body require a compliance review of your breach to get you back to business?
- Do you know what you don’t know?
6. Govern
The Govern function helps organizations set and oversee clear cybersecurity strategies and policies, making sure they align with business goals and risks.
Policy Management
Waident helps businesses create, manage, and maintain clear cybersecurity policies that align with their goals and reduce risk.
Risk Strategy
Waident experts work with you to build a practical cybersecurity risk strategy that protects your business.
3d Party Management
Waident provides oversight and support for third-party cybersecurity risks, helping you manage vendor relationships and ensure your partners meet your security standards.
Compliance Management
Waident assists and manages the process of monitoring and assessing systems to ensure they comply with industry security standards, as well as corporate and regulatory policies.
Contact Us to learn more about cybersecurity before your organization becomes a statistic.
Latest Posts on Cybersecurity
The AI Security Dilemma: What Every CEO Must Know to Protect Their Business
Many CEOs remain hesitant to embrace AI in their company, but the truth is, we are already surrounded by it. As a cybersecurity firm, our top priority is always security—especially when it comes to using tools like AI. What most people don’t know is that AI has been...
Santa’s Gift May Not Be What You Want This Year – Protect Your Company From Hackers During the Holidays
Santa might be getting ready to say “Ho-ho-ho!”, but cybercriminals are gearing up to capitalize on our festive cheer and lowered defenses. As an IT and cybersecurity provider, it’s our duty to warn businesses to be extra vigilant during the holiday season. We...
Email Phishing: How to Recognize, Respond, and Protect Your Data
Almost every week we hear about our clients getting hit with phishing emails and it is scary. Phishing attacks can target anyone, no matter how secure their systems may seem. According to the Sophos Ransomware 2024 report, 59% of companies were hit with ransomware...