We had a client recently ask a good security question. I am paraphrasing, but it went something like: How do I know that someone is not hacked into my network right now and able to get to my data? Sadly the answer was: You do not know. The reality is that with all of the standard security tools and best practices being used by nearly all companies today (complex passwords, MFA, firewall, anti-virus, anti-spyware, spam filtering, Windows updates, etc.) you just do not know since these tools are for preventative measures and none of them are effective 100% of the time. Unfortunately, this leaves a proactive gap for most companies. Leveraging an MDR (Managed Detection and Response) platform can go a long way to letting you KNOW if someone has hacked in and is stealing your data and STOPPING it in real-time.
There have been so many news stories about major security breaches where millions of records were stolen. Nearly all of the breaches happened months or even years before they were found and stopped. Crazy. I think several things led to this lack of security, but mainly it was the fact that the traditional thinking and tools were to blame. Internal IT was doing what they had always done (complex passwords, MFA, firewall, anti-virus, anti-spyware, spam filtering, Windows updates, etc.) and not doing a very good job at that. There were no proactive tools in place so bad things happened.
So what is MDR?
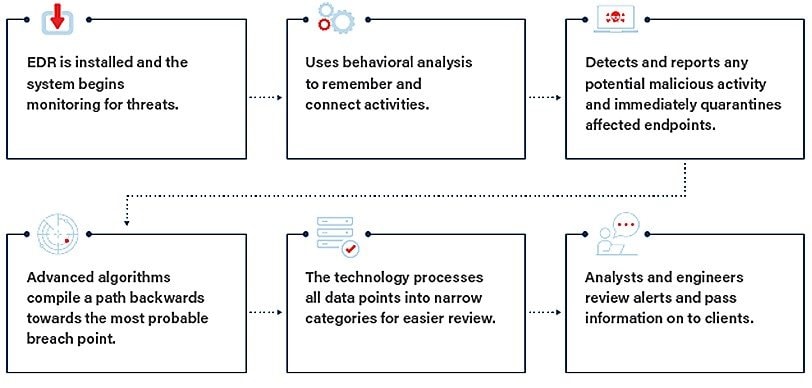
MDR is a proactive approach to security that monitors endpoints in real time and hunts threats that have infiltrated a company’s defenses. An agent monitors computer activity and looks for correlations; when it sees abnormal activity, it sends out an alert with details so it can be investigated.
What does MDR protect your business from?
MDR protects against file-less malware, malicious scripts, or stolen user credentials. It is designed to track the techniques, tactics, and procedures that an attacker uses. But then it goes even deeper. Not only does it learn how attackers break into your network, but it also detects their path of activity – how they learn about your network, move to other machines, and attempt to accomplish their goals in the attack.
You will still need to have the usual tools like a firewall, anti-virus, and the rest of the list mentioned earlier, but maybe it is time to look into MDR. It is a cost-effective solution that can finally help you to stop worrying if a hacker has gotten into your data. Have any questions or want to discuss your security situation?
Send me an email or give me a call and we can discuss this in greater detail.